It’s part of our role as the Government Digital Service to set the standards needed for digital government to be successful.
As we continue to move away from the PSN, we need to think about the new standards we use to share services and exchange data so there is trust in the interaction and integrity in the data.
These new standards could include adopting technical controls like using standards-based approaches to email security and encrypting web transactions using Transport Layer Security (TLS). They could also include leveraging commodity edge devices and/or using Virtual Private Networks (VPNs).
Some of these approaches are already being adopted. Secure email, for example, is a popular PSN alternative with almost 200 public sector bodies as users, and more to follow over the coming year as we continue to encourage migration away from legacy gsi domain names.
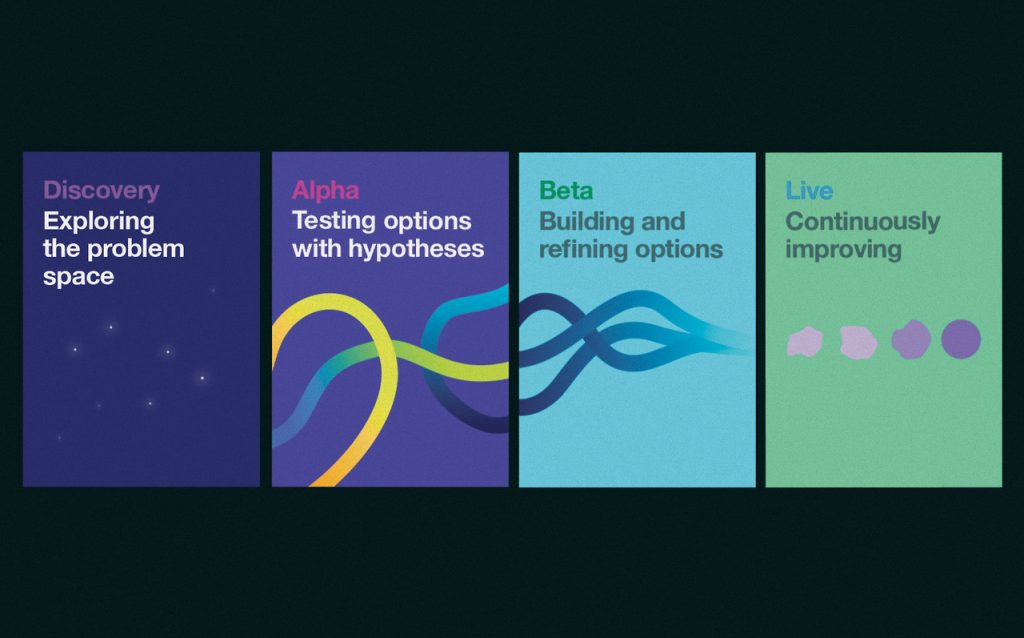
Before we move ahead with an assurance alternative though, we’ll need to test each approach. All new projects at GDS follow the government design principles, including the first one – start with user needs. We’ll be holding a discovery to find out which solution/s will most satisfy users. And an alpha to prototype some of the ideas from the discovery outputs.
Discovering what we need
A discovery is about understanding the user journey. Our project discovery will involve user research into the types of standards and guidance we need now we have begun moving away from the PSN to the internet. We need to make sure users feel supported and create a secure structure for different parts of government to communicate, both local and central.
We need to understand:
- which government users need to exchange data securely
- the needs of these users, how we can meet them and any needs we’re not meeting (we’ll work closely with departments and their digital teams to analyse and articulate new user needs)
- what technology and services are currently meeting users’ needs
- how we can gather and analyse data from the PSN (such as basic network traffic and security vulnerabilities) to inform the applications being used
- how we should start developing solutions for the new future network
- how we can encourage suppliers to work with us to develop common standards for the new network so all suppliers can participate equally and fairly in the new marketplace (this stage will most likely involve interviews with suppliers)
- how organisations can verify their networks to meet the new set of standards we adopt
We’re currently hiring a multidisciplinary team for this discovery, including: user researchers; specialists in network scanning and analysis, networking technology and the marketplace; and security countermeasure specialists. We’ll also be using one of our in-house data analysts experts to look into all the PSN data.
This discovery team will help set the direction for government network strategy for the foreseeable future. They’ll have privileged access to specialists across the public sector. If you are interested in the opportunity (you’ll need to be SC cleared), please see the Digital Marketplace for more details.
The discovery will comply with our Cloud First policy, Network Principles and previous acknowledgement that the internet is ‘ok’.
The next step: beginning an alpha
Following the discovery, we’ll use an alpha to prototype the ideas we’ve discovered. This will involve testing the technology with users, identifying any problems and deciding how these can be solved. We’ll also look at the costs and risks involved with any new technology or standard we’re adopting.
By the end of this alpha, in around 6 months time, we should have a good understanding of how we can assure connections for a wide range of public sector organisations using the best available standards-based approaches. We’ll then move into beta.
Working with suppliers
During the discovery and alpha, we’ll keep in touch with network users and commercial providers to make sure those who need to make decisions get clear information. We’ll also be working closely with the National Cyber Security Centre (NCSC) and the Crown Commercial Service (CCS) to ensure we will still have the widest possible range of suppliers when buying network services.
We’re really keen to create a healthy supplier market around the technology we use to establish high-quality connections, just as we did with PSN. We’ll be setting the standards but will look to suppliers for guidance. For example, if it’s commodity edge devices that we’re using, we’d ask suppliers in this space for advice on implementation and configuration.
It’s also important that industry works together with us to develop common standards that don’t prevent any suppliers from participating in the marketplace. At the moment government organisations can buy a PSN connection from dozens of suppliers and this connection will work with PSN connections from their competitors. This interoperable framework needs to continue under the new assurance network so we can continue to see the performance and security benefits.
To make sure you stay up to date with all the latest developments, you can sign up to alerts from the GDS Technology blog.
If this sounds like a good place to work, take a look at Working for GDS - we're usually in search of talented people to come and join the team.

3 comments
Comment by OS posted on
Lots here and in the previous linked blog posts about Integrity and establishing trust and protecting the confidentiality/privacy of data - but these are in fact the easy parts of the equation.
I see very little discussion around the hard stuff over Internet, such as guaranteed Availability, traffic prioritisation, assured delivery/routing controls, QOS, etc.
Unlike the "C" and "I" aspects, the availability challenges of connecting over Internet for business critical services don't appear to have moved on appreciably since the use of Internet was examined and firmly discounted in the Home Office work to replace CJX back in 2011?
In the simplest terms - the Police (and other Blue Light services) require high availability networks as much (and sometimes more) than maintenance of Confidentiality and Integrity. (A & C are high, Integrity is often accepted as being less assurable - and they have business processes in place to handle that in most practical circumstances).
So one of your key questions has to be what work can feasibly be done to establish high availability links over Internet for business or mission critical services (especially during times of national stress or major incident)?
If that question cannot be answered then you effectively rule out any sector with high availability requirements from reliance on Internet bearers as their core networking infrastructure.
Secondly - and whilst I know that under GSCP we don't really care too much about attacks from FIS or other capable attackers (or at least at OFFICIAL we profess not to be seeking to apply specific protections ) - can this adoption of Internet connections for core business services really be sensibly applied in a landscape where DDOS and complex blended attacks are commonplace? Will Ministers, SRO's and SIRO's all sign off on accepting risks of loss of functionality in core HMG services (and is it even possible for those subject to NIS to do so?)
Internet may well look 'OK' in strictly theoretical terms, but when the cost of all the necessary 'optional extras' to protect organisations connecting to Internet with sufficiently resilient and protected gateways robust enough to transact their core business functions are taken into account, I suspect it would be a lot cheaper and easier to just buy a higher spec model of network in the first place (i.e. a commercial MPLS or similar variant)?
There may well be a place for hybrid WAN approaches, especially within organisations that have 'branch office' legs that are not business core and where risks can be accepted of course, though thats probably going to have to be established on an org by org basis.
As a novel idea, we could also just try reverting to the original proposals of the network of networks strategy paper written in 2005 (which was quite different to what PSN ultimately became) and re-build our network connections based on communities of interest and just gateway them together with something like the GCF/GCN type services we have today.
At least then you would have a model designed specifically to both allow and remove excuses not to collapse and consolidate networks within sectors and reduce duplication of services. Promoting re-use of assets within specific groups of organisations all handling the same type of data and facing the same risks or legislative obligations will drive costs down and facilitate data sharing at source without having to move data back and forth across so m any network links - more data sharing happens intra-community rather than inter-community after all.
For the Criminal Justice sector in particular this would now seem particularly appropriate - they effectively work under their own bespoke DPA 2018 provisions now anyway (DPA 2018 Part 3) and for the first time 'Police data genuinely IS special' - and defined as such by Act of Parliament no less...
Comment by khidr posted on
Hi OS,
Thank you for your comments. We intend to be thorough with our discovery, and would expect our work to explore some, if not all of these points.
Khidr
Comment by Mark posted on
With respect to A at a basic level(+ I and C to a lesser degree), what is the plan to avoid BGP hijacking for example?